
Check Point Endpoint Remote Access VPN Software
Simplifies endpoint security management
Provide users with secure, seamless remote access to corporate
networks and resources when traveling or working remotely.
Privacy and integrity of sensitive information is ensured
through multi-factor authentication, endpoint system compliance
scanning and encryption of all transmitted data.
Overview:
Provide users with secure, seamless remote access to corporate networks and resources when traveling or working remotely. Privacy and integrity of sensitive information is ensured through multi-factor authentication, endpoint system compliance scanning and encryption of all transmitted data.
 What is Remote Access VPN?
What is Remote Access VPN?
Remote Access VPN ensures that the connections between corporate networks and remote and mobile devices are secure and can be accessed virtually anywhere users are located.
A secure remote access solution promotes collaboration by connecting global virtual teams at headquarters, branch offices, remote locations, or mobile users on the go.
Each host typically has VPN client software loaded or uses a web-based client. Privacy and integrity of sensitive information is ensured through:
- Multi-factor authentication
- Endpoint system compliance scanning
- Encryption of all transmitted data

Secure Remote Access
Securely and privately access your data from anywhere with VPN

Simple User Experience
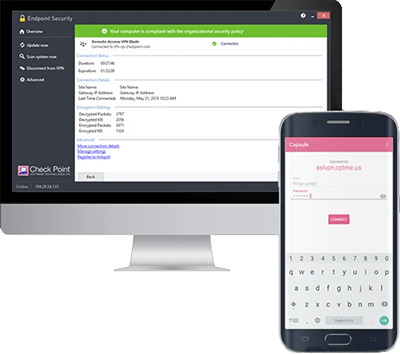
Connect securely from any device

Integrated
Configure policy and view VPN events from one console
Remote Access Products
Remote access is integrated into every Check Point network firewall. Configure client-to-site VPN or set up an SSL VPN Portal to connect from any browser.
IPsec VPN
Provides full access to the corporate network with a VPN client.
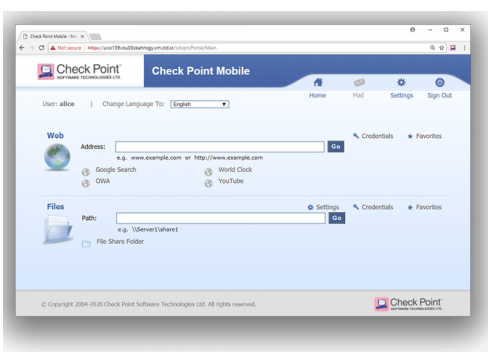
SSL VPN Portal
Provides web-based access without the need to install a VPN client.
Benefits:
Secure access to corporate resources while traveling or working remotely
- Full IPsec VPN connectivity for strong authentication and data integrity
- Endpoint compliance scanning protects from malware and intrusions
Simple user experience
- Seamless roaming between networks and automatic session configuration
- Re-establishes lost connections by automatically switching connection modes
Integrated into Check Point Software Blade Architecture
- Activate endpoint remote access protection on any Check Point gateway
- Centrally-managed endpoint solution
Features:
VPN Auto-Connect
VPN auto-connect re-establishes lost connections by automatically switching connection modes. It eliminates the need for users to re-authenticate when roaming between different network types (LAN, WiFi, GPRS, etc.), using intermittent networks or resuming work from sleep mode.
Multi-Factor Authentication Support
The Endpoint Remote Access VPN Software Blade offers comprehensive authentication, including:
- Username and passwords (including cached passwords)
- SecurID
- Challenge / Response
- CAPI software and hardware tokens
Secure Hotspot Registration
With secure hotspot registration, administrators can selectively grant access to hotspot registration sites. Hotspot registration pages are loaded automatically for the user.
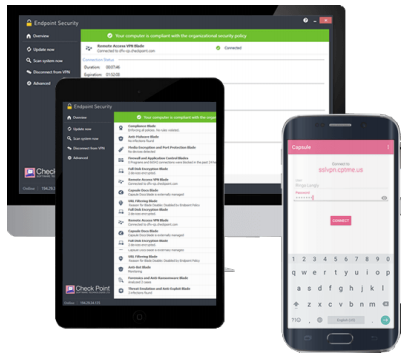
Integrated into Check Point Software Blade Architecture
The Endpoint Remote Access VPN Software Blade is integrated into the Software Blade Architecture. Endpoint Security Software Blades from Check Point bring unprecedented flexibility, control and efficiency to the management and deployment of endpoint security. Choose from six Software Blades to deploy only the protection you need, with the freedom to increase security at any time from a single central management console.
IPsec VPN
Check Point Endpoint Remote Access VPN Software Blades support full IPsec VPN connectivity for strong authentication, data integrity and confidentiality. NAT-T standard support enables traversing between static and dynamic Network Address Translation (NAT) devices.
Compliance Scanning
With compliance scanning, endpoints are automatically scanned for malware and suspicious activity to ensure compliance with corporate security policies. Failing endpoints can be directed to remediation.
As an example, administrators can ensure that endpoints are free of malware and have the latest service packs installed before granting access to corporate resources.
Central Management
The Endpoint Remote Access VPN Software Blade is centrally managed by the Endpoint Policy Management Software Blade, enabling central policy administration, enforcement and logging from a single, user-friendly console. Centralized management offers unmatched leverage and control of security policies and multiple deployment options offer easy installation and minimize user impact, for a reduced overall cost of operations.
Secure Remote Access:
Compliance Scanning
Endpoint compliance verifies the security level of the endpoint, and reports back to the Security Gateway. The gateway can allow connectivity to specific network resources, based on compliance level.
Deployment Options
Install our endpoint VPN client in one of three options.
-
Included in Endpoint Security (Windows, macOS)
- Firewall
- Application Control (not available on macOS)
- Remote Access VPN
- Compliance
- Standalone Check Point Mobile for Windows
- Remote Access VPN
- Compliance
-
Standalone SecuRemote
- Remote Access VPN
Central Management
Remote Access VPN is centrally managed, enabling central policy administration, enforcement and logging from a single, user-friendly console. Centralized management offers unmatched leverage and control of security policies.
Mobile Access Option
The Web Portal is best for connecting securely to corporate resources from a web browser. Through an integrated web portal, users can access native corporate applications including web-based resources, shared file and email. Administrators can customize the design of the web portal to match their corporate brand identity.
Specifications:
| Specifications | |
|---|---|
| Secure Access |
|
| Authentication Support |
|
| Seamless Tunnel Establishment, Teardown |
|
| Remote Access Options | |
| Connect Options | Hotspot detection, Office Mode IP, Split Tunneling, Hub Mode, automatic fallback from NAT-T to HTTPS |
| SSL VPN Portal |
|
| Layer 3 VPN Tunnel |
|
Documentation:
Download the Check Point Endpoint Remote Access Datasheet (PDF).

