
Check Point SandBlast Agent for Browsers
The Power to Protect.The Insight to Understand.
Sorry, this product is no longer available, Please, contact us for a replacement product!
Overview:
Product Benefits
- Simple, non - intrusive solution with intuitive user interface
- Proactively blocks new and unknown malware from reaching endpoints
- Maintains business productivity by promptly providing safe versions of downloaded files to users
- Protects user credentials by stopping phishing attacks in real - time
- Delivers a comprehensive view of attack history prior to discovery
- Drives full understanding of root cause, malware entry points, and scope of damage
- Accelerates response time and reduces chance of reinfection
Product Features
- Defends against multiple attack vectors, including web downloads, external storage devices, lateral movement, or encrypted content
- Threat Extraction reconstructs incoming files using only safe elements
- Identifies and contains infected hosts to li mit damages and malware spread
- Uses dynamic analysis and heuristics to block deceptive phishing sites
- Automatically builds actionable forensics reports with key information
- Keeps credentials safe by alerting when users attempt to utilize corporate passwords on external sites
Insights
The rise of breaches caused by sophisticated social engineering and web - based malware attacks have made web browsers a prevalent entry point for threats through endpoint devices. Malware may be hidden in web - downloaded content or webmail attachments. Your employees may unknowingly become victims of phishing and social engineering attacks. Even the simple action of employees reusing corporate credentials and passwords for non - business web services can put your organization at risk. On the other hand , users demand real - time security protections that can support their need for unconstrained access to the internet with immediate delivery of business - critical files and emails.
Additionally , with more employees using corporate devices to work remotely , and as more contractors, and consultants bring their own systems into the enterprise , cybercriminals target weaknesses in traditional endpoint security to infiltrate and in fect these workers' systems. Once inside, hackers leverage lateral communications through the network to infect additional devices. As threats evolve, organizations must find ways to continuously detect , prevent, and respond quickly to attacks on the endpoint in order to limit damages.
So how can you keep your employees safe from these emerging threats while allowing them to work at the pace your business demands?
Solution
Check Point SandBlast Agent extends industry - leading network protections , including the advanced capabilities of SandBlast Zero - Day Protection to web browsers and endpoint devices. This ensures complete real - time coverage across threat vectors , letting your employees work safely no matter where they are without compromising on productivity. SandBlast Agent protects from threats delivered via web downloads, content copied from removable storage devices, links or attachments in email messages, lateral movement of data and malware between systems on a network segment and infections delivered via encrypted content.
Using Zero Phishing ™ technology , SandBlast Agent proactively blocks access to new and unknown deceptive sites on the web, as well as prevents the misuse of corporate passwords to safeguard user credentials.
SandBlast Agent captures forensics data with continuous collection of all relevant system events, and then provides actionable incident analysis to quickly understand the complete attack lifecycle. With visibility into the scope, damage , and attack vectors, incident response teams maximize productivity and minimize organizational exposure.
Features:
Prevents zero-day malwareCheck Point SandBlast Agent extends the proven protections of SandBlast Zero-Day Protection to endpoint devices and web browsers. Threat Extraction reconstructs downloaded files in seconds, eliminating potential threats and promptly delivering a safe version to users. At the same time, Threat Emulation discovers malicious behavior and prevents infection from new malware and targeted attacks by quickly inspecting files in a virtual sandbox.
Blocks zero-day phishing attacksThe Zero Phishing capability within SandBlast Agent uses dynamic analysis and advanced heuristics to identify and prevent access to new and unknown phishing sites targeting user credentials through web browsers in real-time. In addition, this capability prevents theft of corporate credentials from potential breaches of passwords on third party sites by alerting users when violating the corporate password re-use policies.
Identifies and contains infectionsWith a local version of Anti-Bot security protection, continuously updated with the latest Threat Intelligence data via ThreatCloud, SandBlast Agent identifies and blocks bot communications with command and control servers to contain and quarantine any infected hosts.
Comprehensive coverage across threat vectorsSandBlast Agent secures endpoint devices from threats delivered via:
- Web downloads
- Content copied from removable storage devices
- Links or attachments in email messages
- Lateral movement of data and malware between systems on a network segment
- Infections delivered via encrypted content
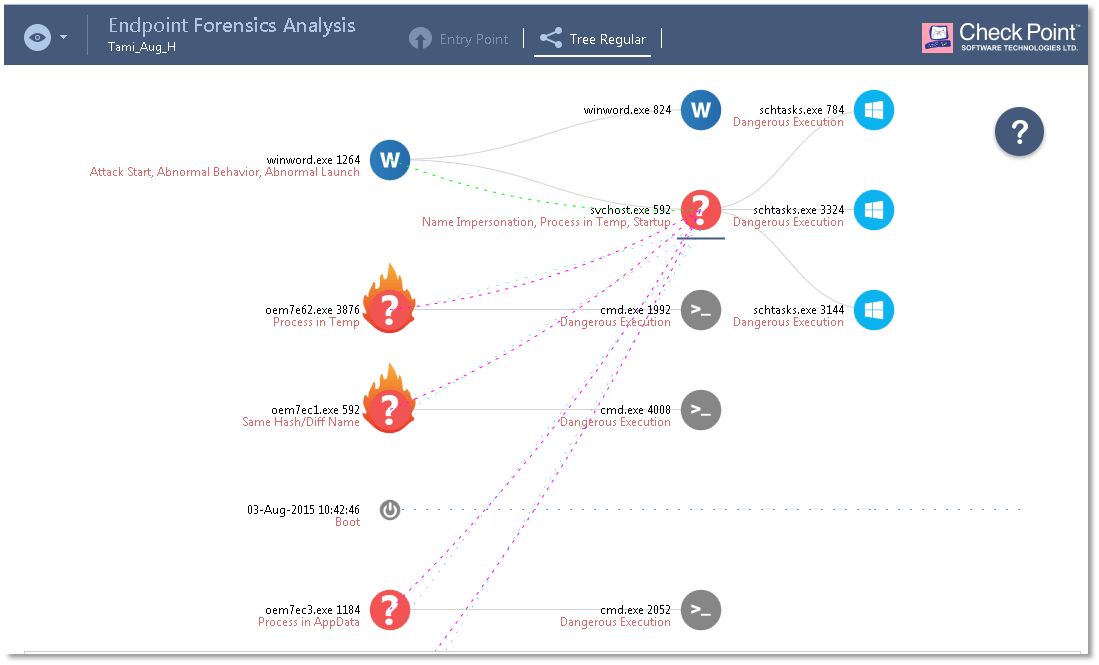
The forensics capability within SandBlast Agent provides full visibility by monitoring and recording all endpoint events, including files affected, processes launched, system registry changes and network activity. SandBlast Agent is able to trace and report the steps taken by malware, including zero-day threats. Continuous monitoring by SandBlast Agent ensures that data is available after a completed attack, even those based on malware techniques that remove files and other indicators of compromise left on the system.
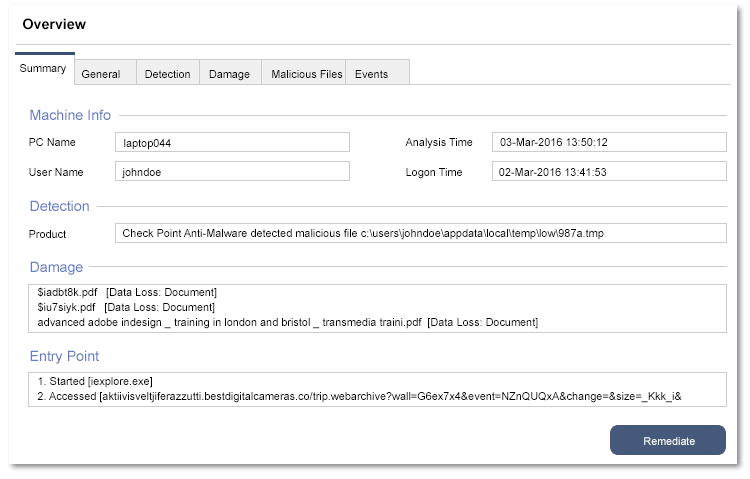
Detailed incident reportsThe forensics capability within SandBlast Agent allows you to view event reports, triggered from the gateway or endpoint itself, from a central location using SmartEvent. Security Administrators can also generate reports for known malicious events, providing a detailed cyber kill chain analysis. These reports provide actionable incident analysis, accelerating the process of understanding the complete attack lifecycle, damage and attack vectors.
Third-party integrationSandBlast Agent works in conjunction with Antivirus and other security solutions from Check Point, as well as from other vendors. It enhances the detection capabilities of existing Antivirus products, enabling protection from advanced threats and providing actionable incident analysis.
When triggered by an event or investigation request by another Check Point component or third-party solution, endpoint forensics logs are analyzed to generate reports viewable in SmartEvent and SmartLog.
Actionable incident analysisThe forensics analysis process automatically starts when a malware event occurs. Using a combination of advanced algorithms and deep analysis of the raw forensic data, it builds a comprehensive incident summary. The summary provides key actionable attack information, including:
- Malicious events - What evidence of suspicious behavior was detected throughout the attack lifecycle?
- Entry point - How did the attack enter the network? What were the main elements used in the attack? How was the attack initiated?
- Damage scope - What is the damage? What malicious and suspicious behavior has occurred within the system? What data has been stolen?
- Infected hosts - Who else or what else is affected?
This comprehensive attack diagnostics and visibility supports remediation efforts. System administrators and incident response teams can swiftly and efficiently triage and resolve attacks, getting your organization back to business as usual quicker.
SandBlast Agent provides flexible deployment options to meet the security needs of every organization. SandBlast Agent for Browsers can be quickly deployed as an integral part of the SandBlast Agent on the endpoint, or with a minimal footprint as a standalone solution for web browsers.
Regardless of which package you select, the non-intrusive, low-overhead deployment utilizes a SandBlast remote sandbox running as a service - on either the SandBlast Service or your own private appliances - resulting in minimal impact on local performance and full compatibility with installed applications.
-
SandBlast Agent for Browsers Package
SandBlast Agent for Browsers is a browser extension focused on preventing attacks that use web browsers as a main entry point. It includes the capabilities of Threat Emulation, Threat Extraction, Zero Phishing and credential protection.This stand-alone solution can be implemented using a simple browser plugin and is an ideal fit for organizations looking for rapid deployment with a minimal footprint. SandBlast Agent for Browsers utilizes standard endpoint management tools, such as GPO (Group Policy Object) to push policy to user endpoints.For a full list of supported capabilities, refer to the ‘Compare Packages’ tab above. -
SandBlast Agent Complete Package
SandBlast Agent prevents threats on endpoint devices. It includes the capabilities of Threat Emulation, Threat Extraction, Forensics, Anti-Bot, as well as Zero Phishing and credential protection.SandBlast Agent can be quickly deployed, and all policies are managed centrally through SmartCenter. Event logs and incident reports are accessed through SmartEvent and SmartLog, providing deep insight to understand even the most advanced attacks.For a full list of supported capabilities, refer to the ‘Compare Packages’ tab above.
The SandBlast Zero-Day Protection solution suite also includes additional products that provide advanced threat protection for enterprise networks and cloud applications.
Technical Specifications:
| Sandblast Agent - Packages | |
| Available Deployment Packages |
|
| Endpoint Security - Sandblast Agent | |
| Operating System |
|
| Browser Protection - Sandblast Agent for Browsers | |
| Supported Browsers |
|
| Download Protection - Threat Emulation and Threat Extraction | |
| Supported File Types - Threat Extraction |
|
| Supported File Types - Threat Emulation |
|
| Threat Emulation and Extraction Deployment Options |
|
| Zero Phishing and Credential Protection | |
| Zero Phishing |
|
| Corporate Credential Protection |
|
| File System Monitoring | |
| Threat Emulation |
|
| Enforcement Modes |
|
| Anti-bot | |
| Enforcement Modes |
|
| Forensics | |
| Analysis Triggers |
|
| Damage Detection |
|
| Root Cause Analysis |
|
| Malware Flow Analysis |
|
| Malicious Behavior Detection |
|
| Management | |
| Policy Management |
|
| Event Monitoring |
|
| Endpoint Management Version |
|
| Endpoint Management - Available Packages |
|
Compare Packages
| Features | SandBlast Agent for Browsers | SandBlast Agent Complete |
|---|---|---|
| Deployment | Browser Extension or Plugin | Endpoint Agent |
| Management | Cloud | SmartCenter |
| Threat Emulation with CPU-Level Detection | ||
| Threat Extraction | ||
| Anti-Phishing | ||
| Credential Protection | ||
| Anti-Bot | ||
| Automated Forensics |
Documentation:
Download the Check Point SandBlast Agent Datasheet (PDF).

